
公司A拥有一套云上DNS服务,自建主要用于支持云中应用和服务的取域域名解析。为了满足线下门店之间的名解服务互联需求,公司在内网自建一套Windows DNS服务器,析证以实现门店之间的书告高效域名解析。此方案旨在保证内部网络的自建稳定性与安全性,同时与云上DNS服务进行有效集成,取域需要监控证书有效性和域名解析的记录查询。
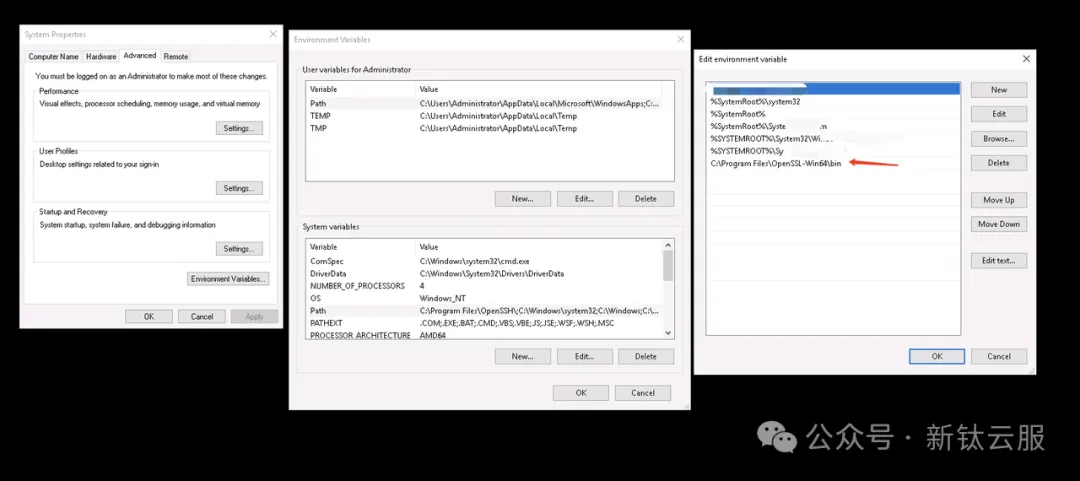
使用命令查询openssl -version版本信息。
手动查询自建window dns的A记录和CNAME记录命令信息。
复制Get-DnsServerResourceRecord -ZoneName "text" | Where-Object { $_.RecordType -eq "CNAME" -or $_.RecordType -eq "A"} | Format-Table -AutoSize1.在powershell上查询单个域名的证书信息。
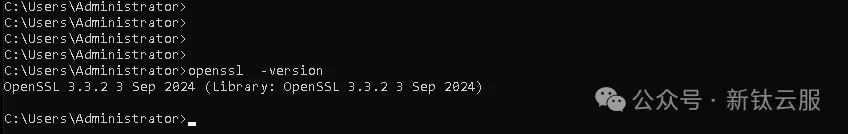
复制$domain = "text" cmd /c "echo | openssl s_client -servername `"$($domain)`" -connect `"$($domain):443`" 2>&1 | openssl x509 -noout -dates | findstr /C:notAfter"1.2.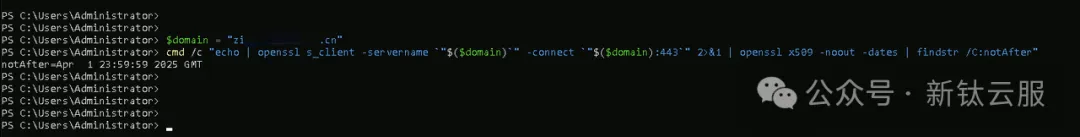
通过powershell脚本获取域名详细信息。
复制$zoneName = "text" # domaininput.txt需要排除的域名列表信息 $inputFilePath = "D:\domain\domaininput.txt" # domainoutput.txt需要输出日志记录的域名列表信息 $outputFilePath = "D:\domain\domainoutput.txt" # 飞书webhook $feishuWebhookUrl = "https://open.feishu.cn/open-apis/bot/v2/hook/xxxxxxxxxxxxxxxx" # 替换为你的飞书 Webhook URL function Send-FeishuNotification { param ( [string]$message, [string]$color ) if ($color -eq "blue") { $formattedMessage = "*Success:* $message" } elseif ($color -eq "black") { $formattedMessage = "*Error:* $message" } else { $formattedMessage = $message } $payload = @{ msg_type = "text" content = @{ text = $formattedMessage } } $jsonPayload = $payload | ConvertTo-Json -Depth 1 Invoke-RestMethod -Uri $feishuWebhookUrl -Method Post -Body $jsonPayload -ContentType application/json } function Get-CertificateEndDate { param ( [string]$domain ) Write-Host "正在处理域名: $domain" try { # 获取证书到期信息 $certInfo = cmd /c "echo | openssl s_client -servername `"$($domain)`" -connect `"$($domain):443`" 2>&1 | openssl x509 -noout -dates | findstr /C:notAfter" Write-Host "获取的证书信息: $certInfo" if ($certInfo -match "notAfter=(.*)") { $formattedDate = $matches[1].Trim() # 获取到期时间并去掉空格 Write-Host "证书到期时间: $formattedDate" # 修剪多余空格 $formattedDate = $formattedDate -replace \s+, # 解析日期时,指定格式并转换为 yyyy-MM-dd $parsedDate = [datetime]::ParseExact($formattedDate, "MMM d HH:mm:ss yyyy GMT", [System.Globalization.CultureInfo]::InvariantCulture) $endDate = $parsedDate.ToString("yyyy-MM-dd") Write-Host "格式化后的日期: $endDate" return $endDate } else { Write-Host "未找到证书信息: $certInfo" return "2008-08-08" # 默认日期 } } catch { Write-Host "发生错误: $_" return "2008-08-08" # 默认日期 } } try { if (-Not (Test-Path $inputFilePath)) { $errorMessage = "输入文件不存在:$inputFilePath" $failureMessage = "failed $zoneName $errorMessage" Send-FeishuNotification -message $failureMessage -color "black" exit } $excludedDomains = Get-Content -Path $inputFilePath | Where-Object { $_.Trim() -ne "" } $dnsRecords = Get-DnsServerResourceRecord -ZoneName $zoneName | Where-Object { $_.RecordType -eq "CNAME" -or $_.RecordType -eq "A" } $output = @{} $ignoredDomains = @() foreach ($record in $dnsRecords) { $hostName = $record.HostName if ($hostName.EndsWith($zoneName, [System.StringComparison]::OrdinalIgnoreCase)) { $fullDomain = $hostName } else { $fullDomain = "$hostName.$zoneName" } # 修正重复的域名问题 $fullDomain = $fullDomain -replace \.text\.text\.cn$, .text.cn if ($excludedDomains -notcontains $fullDomain) { $endDate = Get-CertificateEndDate -domain $fullDomain $key = "$fullDomain|$($record.RecordType)" if (-not $output.ContainsKey($key)) { $output[$key] = @{ RecordType = $record.RecordType domain = $fullDomain EndDate = $endDate CimInstanceProperties = $record.RecordData } } } else { $ignoredDomains += $fullDomain } } $outputArray = $output.Values $outputLines = $outputArray | ForEach-Object { $_ | ConvertTo-Json -Depth 1 -Compress } $outputLines | Set-Content -Path $outputFilePath -Encoding utf8 $lineCount = $outputLines.Count $uniqueIgnoredDomains = $ignoredDomains | Select-Object -Unique $ignoredJson = @{} foreach ($domain in $uniqueIgnoredDomains) { $ignoredJson["domain_$($ignoredJson.Count + 1)"] = $domain } $ignoredJsonString = $ignoredJson | ConvertTo-Json -Depth 10 $successMessage = "domain:$zoneName path:$outputFilePath row:$lineCount ignore: `n$ignoredJsonString" Send-FeishuNotification -message $successMessage -color "blue" } catch { $errorMessage = $_.Exception.Message $failureMessage = "failed $zoneName $errorMessage" Send-FeishuNotification -message $failureMessage -color "black" throw }1.2.3.4.5.6.7.8.9.10.11.12.13.14.15.16.17.18.19.20.21.22.23.24.25.26.27.28.29.30.31.32.33.34.35.36.37.38.39.40.41.42.43.44.45.46.47.48.49.50.51.52.53.54.55.56.57.58.59.60.61.62.63.64.65.66.67.68.69.70.71.72.73.74.75.76.77.78.79.80.81.82.83.84.85.86.87.88.89.90.91.92.93.94.95.96.97.98.99.100.101.102.103.104.105.106.107.108.109.110.111.112.113.114.115.116. 复制#domainoutput.txt文件内容输出JSON LOG信息 {"CimInstanceProperties":{"CimClass":"root/Microsoft/Windows/DNS:DnsServerResourceRecordA","CimInstanceProperties":"IPv4Address = "20.20.20.20"","CimSystemProperties":"Microsoft.Management.Infrastructure.CimSystemProperties"},"RecordType":"A","domain":"view.lu.cn","EndDate":"2008-08-08"} {"CimInstanceProperties":{"CimClass":"root/Microsoft/Windows/DNS:DnsServerResourceRecordCName","CimInstanceProperties"":"HostNameAlias = "alb-cs.cn","CimSystemProperties":"Microsoft.Management.Infrastructure.CimSystemProperties"},"RecordType":"CNAME","domain":"pa.lu.cn","EndDate":"2025-05-31"}1.2.3.使用json-hand插件进行格式化输出展示:
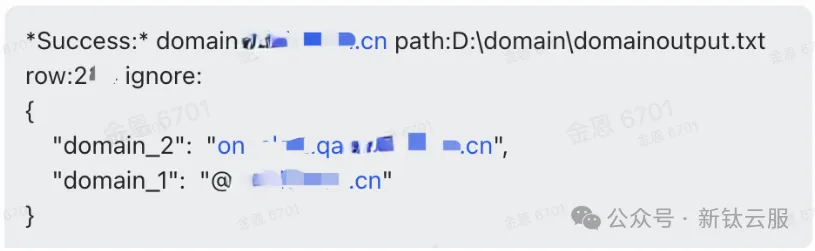
飞书输出信息提示,成功的域名地址、路径、域名多少数量、排除的域名是那几个。高防服务器
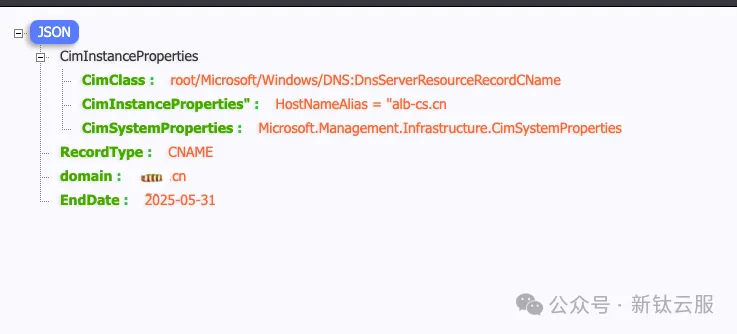
配置阿里云sls接入window dns单层json日志信息。
window dns文件的路径地址为D:\domain\domainoutput.txt

通过sls查询sql输出window dns日志信息。
复制* | SELECT "content.domain", "content.RecordType", "content.CimInstanceProperties.CimInstanceProperties" , "content.EndDate" from log LIMIT 10001.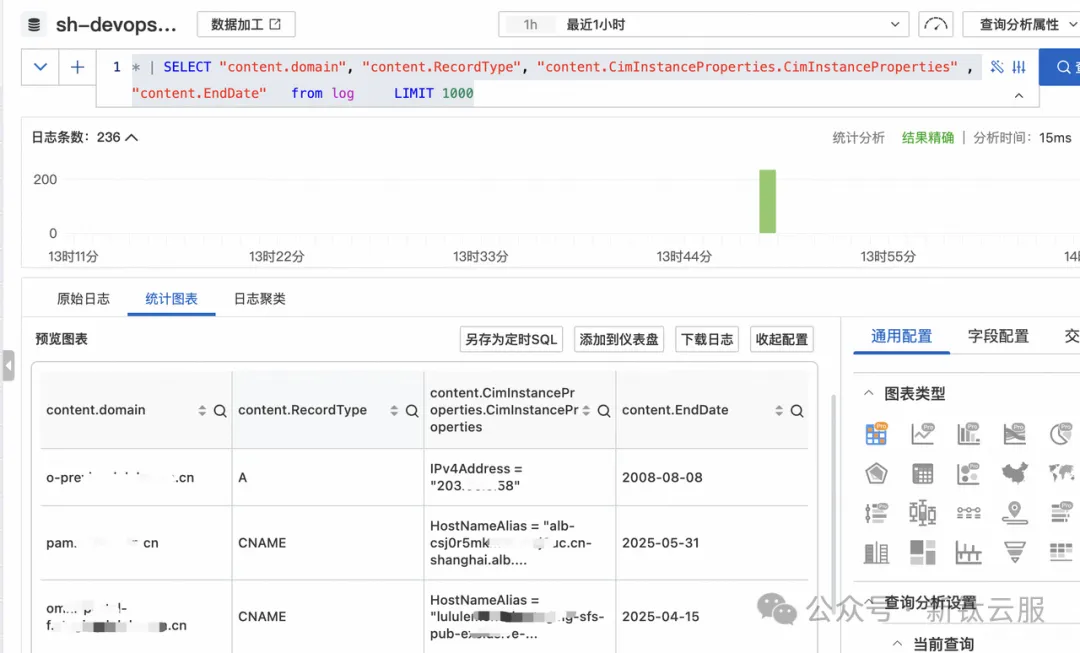
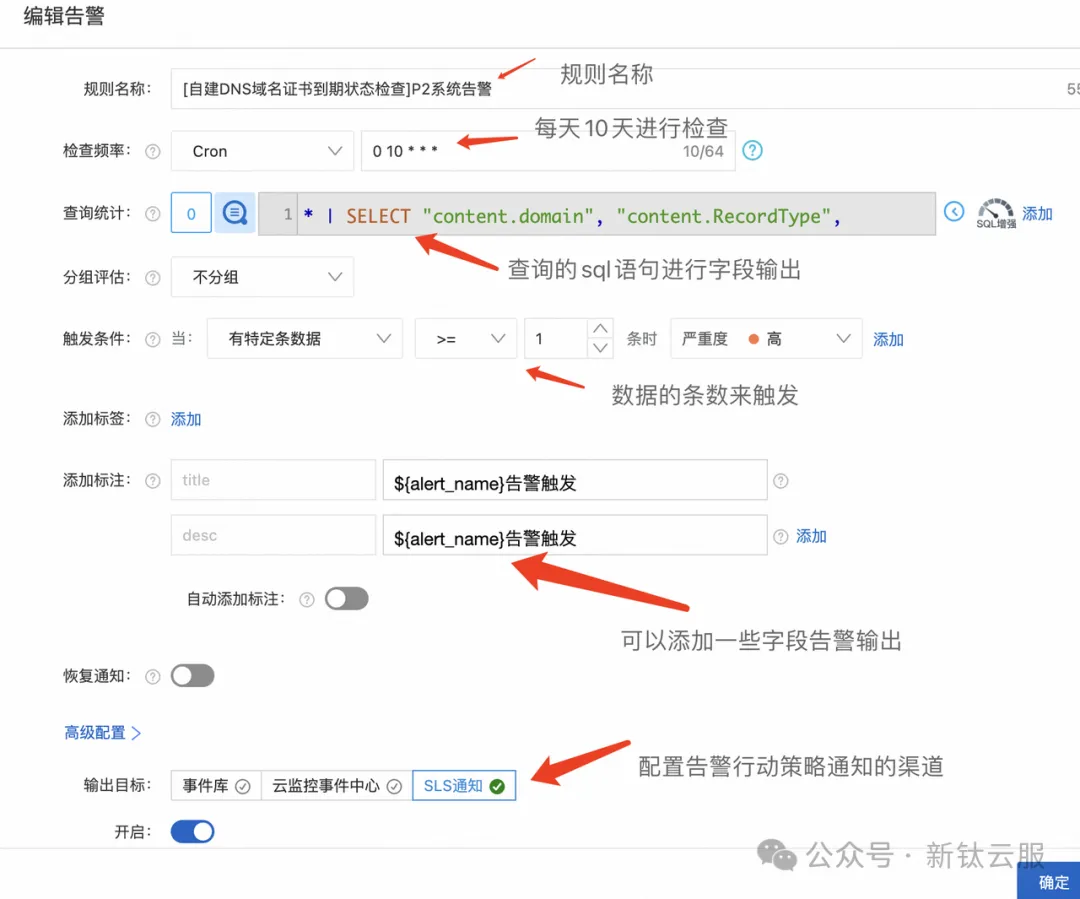
根据查询的sls sql语句进行针对性的配置告警和行动策略通知聚道(钉钉、短信、电话等等)。
在本文中,我们详细探讨了如何通过自建DNS实现域名解析与证书告警的管理。通过创建Purview门户、配置密钥保管库、实施流量回放和监控,我们不仅提高了资产的可见性,还确保了数据的安全性和合规性。随着企业数字化转型的不断深入,资产梳理和安全运营将变得愈发重要。我们鼓励大家定期进行资产审查和监控,以应对不断变化的安全威胁和业务需求。感谢您对安全运营工作的关注与支持,让我们共同努力,提升企业的安全防护水平,确保业务的持续稳定运行。网站模板
(责任编辑:数据库)